Introduction
Blockchain is often described as “unhackable,” a buzzword that helped build trust in cryptocurrencies and decentralized systems. In reality, however, blockchains are not inherently immune to hacks. What blockchain technology does provide is a different set of security trade-offs compared with traditional centralized systems. Understanding where blockchains are strong — and where they are vulnerable — is essential for anyone using or building on this technology.
How blockchain improves security (briefly)
At a high level, a blockchain is a distributed, immutable ledger. Transactions are bundled into blocks and cryptographically linked to previous blocks, so changing a past record requires rewriting all subsequent blocks. Consensus algorithms (like Proof of Work or Proof of Stake) ensure that network participants agree on the canonical history. These properties make tampering expensive and detectable, which significantly raises the bar for attackers.
So where are the weaknesses?
1. Consensus attacks (e.g., 51% attack)
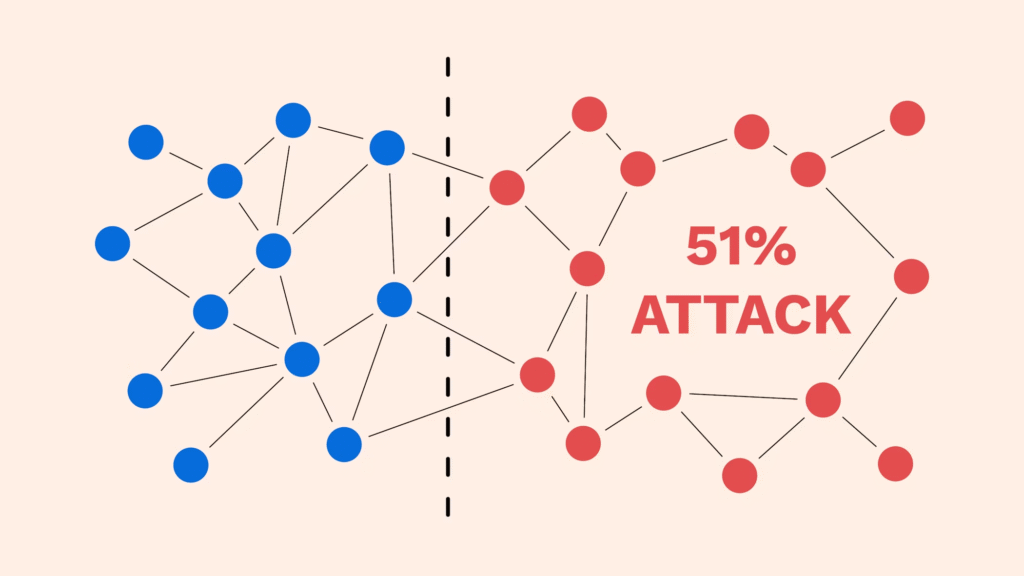
If an attacker controls a majority of the network’s validating power, they can reorganize blocks, double-spend coins, or censor transactions. This is called a 51% attack (or majority attack). It is easier on smaller, low-hashrate blockchains where acquiring majority power is cheaper. Even if difficult for major networks like Bitcoin or Ethereum, smaller chains and poorly secured proof-of-stake networks have experienced such attacks.
2. Smart contract vulnerabilities

Blockchains that run programmable code (smart contracts) inherit software bugs. Vulnerabilities in contract logic—reentrancy, integer overflows, bad access control, flawed randomness, and more—have led to large losses. The DAO hack (2016) and numerous DeFi exploits show that even correct-sounding economic logic can be attacked when implementation errors exist. Once exploited, stolen funds are often irreversible if the blockchain’s immutability prevents rollbacks.
3. Private key theft and wallet compromises

Blockchain security depends on private keys. If a user’s private key is stolen, an attacker can sign transactions and drain funds. Common attack vectors include phishing, malware, insecure key storage, compromised custodial services, and social-engineering. This is the most frequent “hack” experienced by users because the blockchain itself didn’t fail—access controls did.
4. Supply-chain and client software bugs
Nodes, wallets, and infrastructure software can contain vulnerabilities. A compromised wallet app, malicious update, or tampered library can allow attackers to steal keys or manipulate transactions. Even widely used node implementations can be targets if bugs are discovered and exploited.
5. Bridge and cross-chain vulnerabilities

Bridges that move tokens between blockchains are complex and often custodial or trust-based. Many high-profile breaches in DeFi have targeted bridges because they combine smart contracts, multisigs, and off-chain components—each a potential failure point.
6. Sybil, Eclipse, and networking attacks
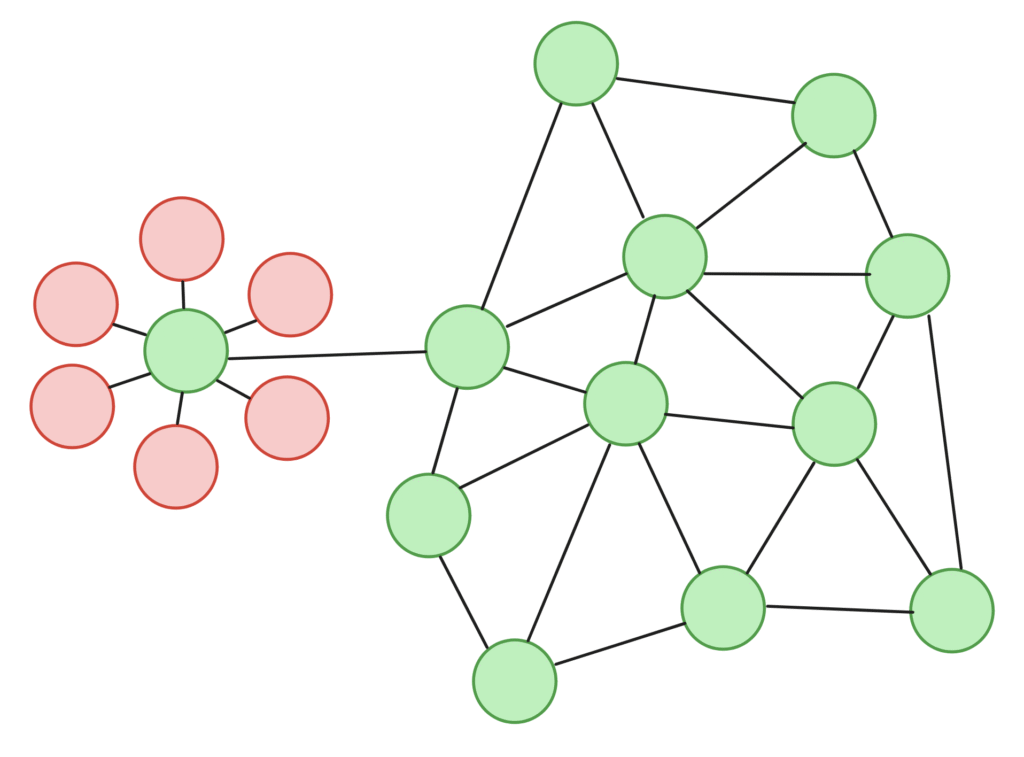
Attackers can attempt to isolate nodes (eclipse attacks), flood the network with fake identities (Sybil attacks), or intercept traffic (BGP routing attacks) to disrupt consensus or manipulate a subset of nodes. These are harder but not impossible, especially against poorly connected nodes or smaller networks.
7. Economic and governance attacks
Proof-of-stake networks can face long-range attacks, bribery of validators, or governance manipulation where protocol upgrades are pushed through maliciously. Economic incentives also matter: if validating honest behavior becomes unprofitable, security can degrade.
Real-world examples (what has happened)
- 51% attacks have been successfully executed on smaller cryptocurrencies where attackers briefly controlled majority hashing power and double-spent coins.
- Smart contract/DeFi hacks repeatedly drain hundreds of millions across various protocols due to logic bugs or misconfiguration.
- Wallet and exchange compromises (via phishing or internal failures) have led to significant user losses even when the underlying blockchain remains secure.
Can these risks be mitigated? — Yes, but not completely eliminated

- Strong cryptography & decentralization: Larger, well-distributed networks are harder to attack. More miners/validators and geographically diverse infrastructure increase security.
- Code audits & formal verification: Rigorous audits, bug bounties, and formal methods reduce smart-contract risk but cannot guarantee zero bugs.
- Secure key management: Hardware wallets, multisignature wallets, secure enclaves, and good operational security practices protect private keys.
- Layered defenses: Rate limits, circuit breakers, multisigs, and timelocks in contracts make large thefts harder and give time to respond.
- Economic design: Carefully designed incentives for validators and slashing conditions reduce malicious behavior.
- Improved network hygiene: Secure node setups, diversified peers, and protections against routing attacks reduce network-level risks.
- Regulatory and custodial standards: Exchanging best practices, audits, and legal frameworks can improve operator security for custodial services.
Conclusion
Blockchains are robust, but not invincible. The ledger itself provides strong guarantees that make tampering expensive and detectable, but the ecosystem around it—smart contracts, wallets, bridges, exchanges, and user practices—introduces many real attack surfaces. Most high-profile “crypto hacks” exploit human error, software bugs, or poorly designed protocols rather than fundamental cryptographic flaws in the blockchain concept.
For users and builders, the right approach is defense-in-depth: assume vulnerabilities exist, apply strict key management, audit code, decentralize infrastructure, and design economic incentives carefully. With those measures, blockchain systems can be highly secure—but absolute immunity to hacking remains, for now, a myth.


